
Oracle is an Organization Member of the Internet Society. We welcome this guest post announcing a new tool that complements our work to improve the security of the Internet’s routing infrastructure.
We are proud to announce the launch of the IXP Filter Check, which is designed to improve Internet routing security by monitoring route filtering at Internet Exchange Points (IXPs). Here we describe the origin of this project, how it works, and what it hopes to achieve.
Background
Last year, Oracle started partnering with the Internet Society to explore ways to make the Internet safer and more secure for our enterprise customers and users. Businesses – banks, insurance companies, pharmaceutical firms – as well as non-profit organizations and governments continue to turn to Internet-facing assets as key components of their critical infrastructure. Market research firm IDC estimates that 55.9 billion devices will be online by 2025. We believe it is incumbent upon us, as trusted partners and suppliers, to help make the global Internet as safe as possible.
Securing trust-based Internet routing is one such security challenge. Despite decades of research and engineering on the topic, securing Internet routing remains a notoriously difficult task. The challenge is evidenced by the fact that nearly every month there is another major story of a disruptive BGP routing incident.
Routing mistakes will inevitably occur as long as people configure routers. Our best hope at containing these incidents is deploying layers of route filtering at key junctions of the Internet. Those junctions fall into two categories: network operators and IXPs.
With respect to network operators, large telecoms have begun announcing their plans to implement the Resource Public Key Infrastructure (RPKI), which is very encouraging. As for IXPs, there is an active movement within the IXP community to filter routes exchanged at route servers based on RPKI and other best practices. With its announcement of its IXP program last year, the MANRS Initiative broadened the scope of its secure routing initiative beyond network operators.
Filtering at Route Servers
Implementing route filtering at IXPs offers the opportunity to make real progress in the improvement of Internet routing hygiene. IXPs serve a vital role in the infrastructure of the Internet by facilitating thousands of connections between the networks of telecoms, content providers, and other major businesses.
However,
the implementation of route filtering can be complicated and to date there has
been no way to independently and programmatically verify whether an IXP was appropriately
filtering its routes. Using data graciously published by Packet Clearinghouse (PCH) and data processing
supported by Oracle Cloud Infrastructure, the Oracle Internet Intelligence team
developed IXP Filter Check to analyze route filtering at nearly 200 IXPs
around the world.
By
monitoring the routes passed by route servers at these IXPs, and identifying
those routes that should have been filtered, IXP Filter Check identifies
gaps in route filtering and aims to assist in technical compliance of MANRS IXP
requirements.
In the course its development, IXP Filter Check has identified major filtering misconfigurations at three IXPs including a month-long RPKI filter outage at one of the world’s largest IXPs. By detecting these problems, IXP Filter Check enabled cooperating route server administrators to fix their route filtering and also validated the need for third party technical review of route server filtering.
What is IXP Filter Check?
Essentially,
IXP Filter Check is a table of metrics observed in BGP messages collected by
PCH at various IXPs in the previous day. The table (see below) reports the
unique number of prefix/origin pairs, messages that were RPKI invalid, or those
lacking a route object (IRR registration) at the time of collection, as well as
prefixes and ASNs that are either bogons or on Spamhaus droplists.
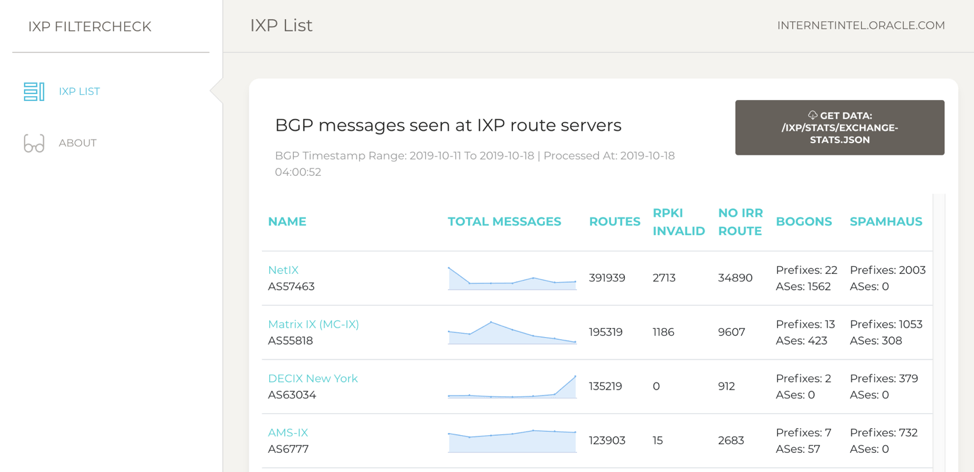
Note
that acting on Spamhaus droplists is not a MANRS IXP requirement, but after
last year’s experience of removing Bitcanal
from IXPs, we felt it was important to include reports of questionable routing to
the IXPs.
One
can click on an IXP to see the individual prefixes being reported as
potentially problematic. In that view, one can expand each prefix to reveal
recent raw BGP messages which include timestamp and BGP community information
as depicted below:
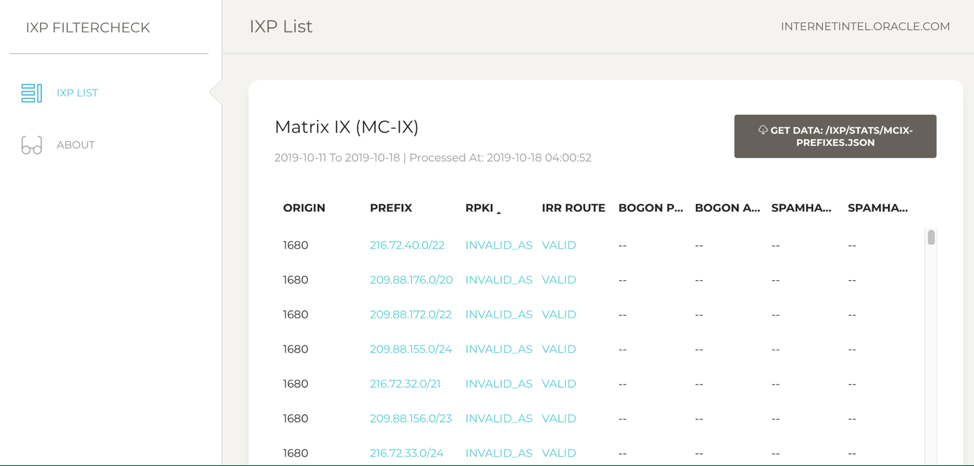
Finally,
one can click on either the RPKI or IRR assessment (“INVALID_ASN” or “VALID” in
the example above) to be taken to an external source to verify the claim.
Conclusion
The IXP program is an important component of the MANRS initiative that strives to prevent Internet disruptions caused by adverse routing incidents. It is no longer an unthinkable goal for all Tier 1 carriers and major IXPs to drop invalid RPKI messages.
Moreover,
if your organization hasn’t created Route Origin Authorizations (ROAs) for its
routes, please consider doing so. This will help enable RPKI filtering to
prevent routes from being affected during a routing mishap. Find your regional
RIR (listed below) and follow their instructions for creating ROAs.
Oracle is committed to helping make the Internet safer and more secure for enterprises and global users and we are proud to contribute this tool to assist IXPs in improving routing security. We thank PCH and the Internet Society for being strong partners in these efforts.
The post Securing the Internet: Introducing Oracle Internet Intelligence IXP Filter Check appeared first on Internet Society.
